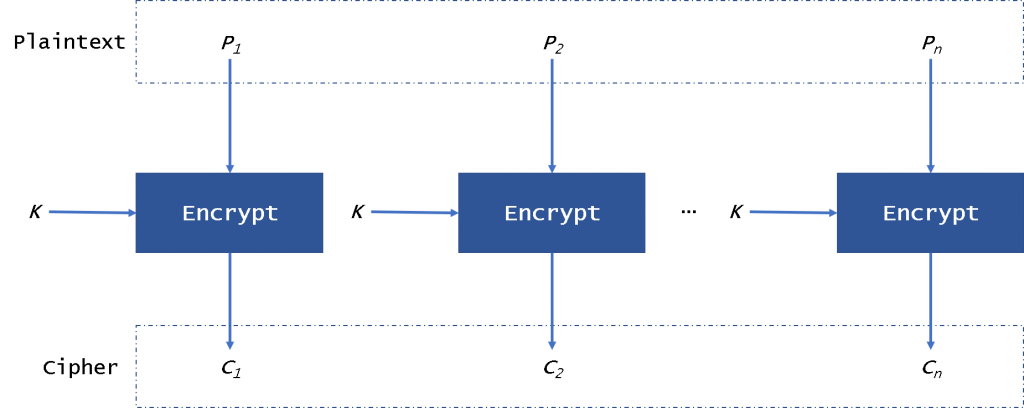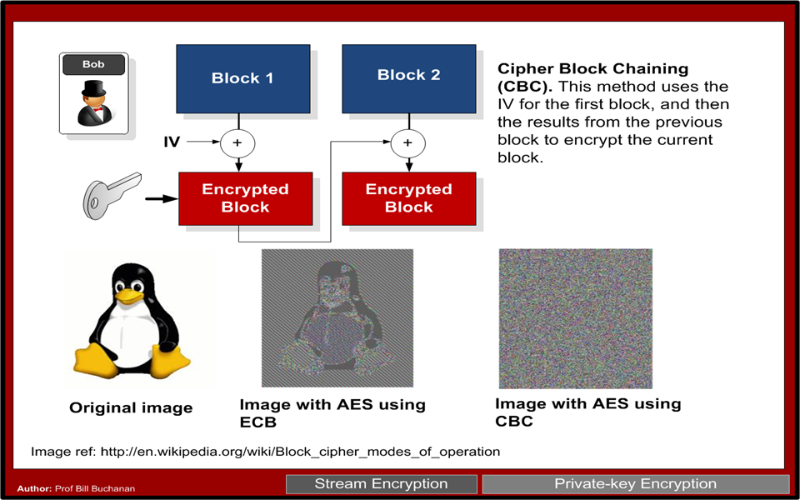
Electronic Code Book (ECB) and Cipher Block Chaining (CBC) | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium

encryption - When using AES and CBC, is it necessary to keep the IV secret? - Information Security Stack Exchange
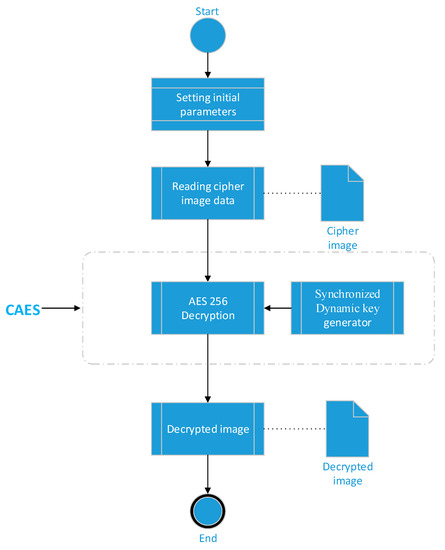
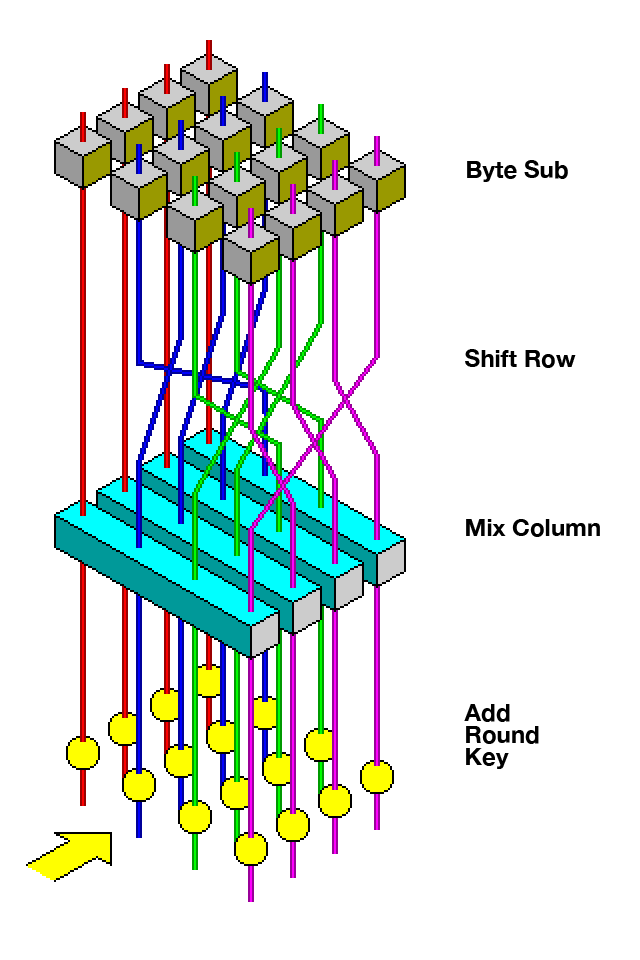
Applied Sciences | Free Full-Text | Chaos-Based Synchronized Dynamic Keys and Their Application to Image Encryption with an Improved AES Algorithm

Cryptopals: Exploiting CBC Padding Oracles | NCC Group Research Blog | Making the world safer and more secure
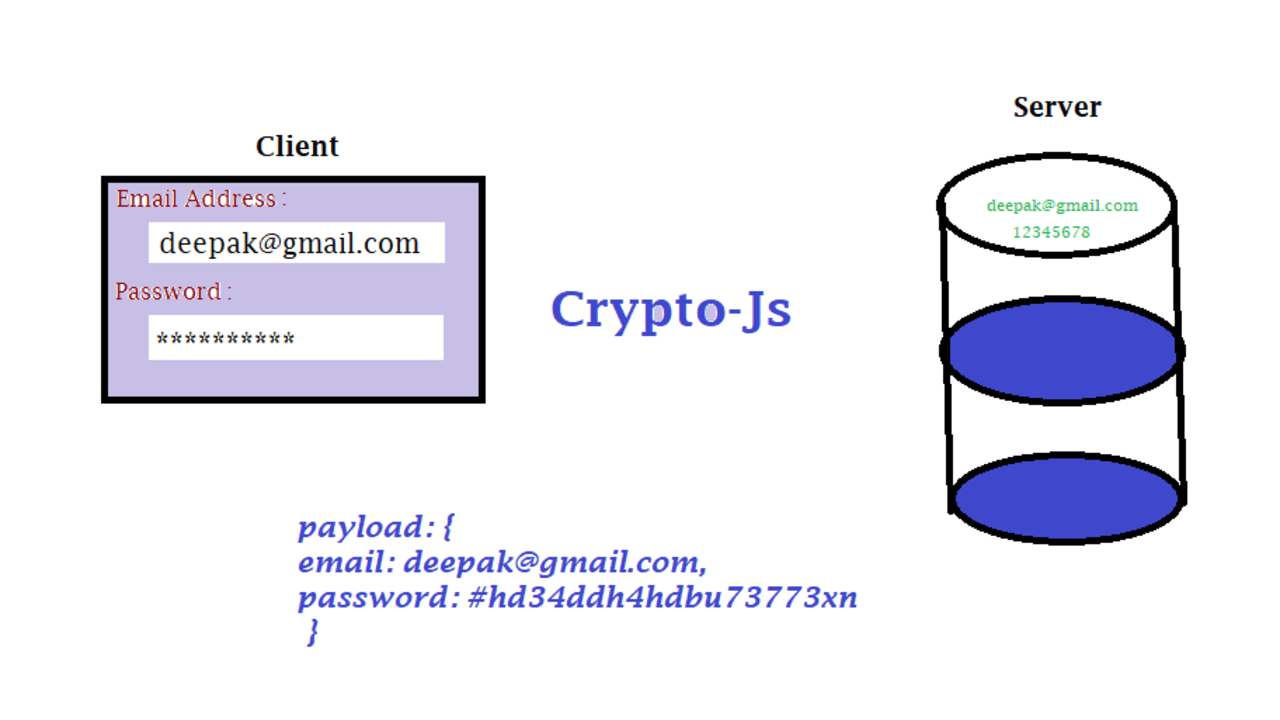
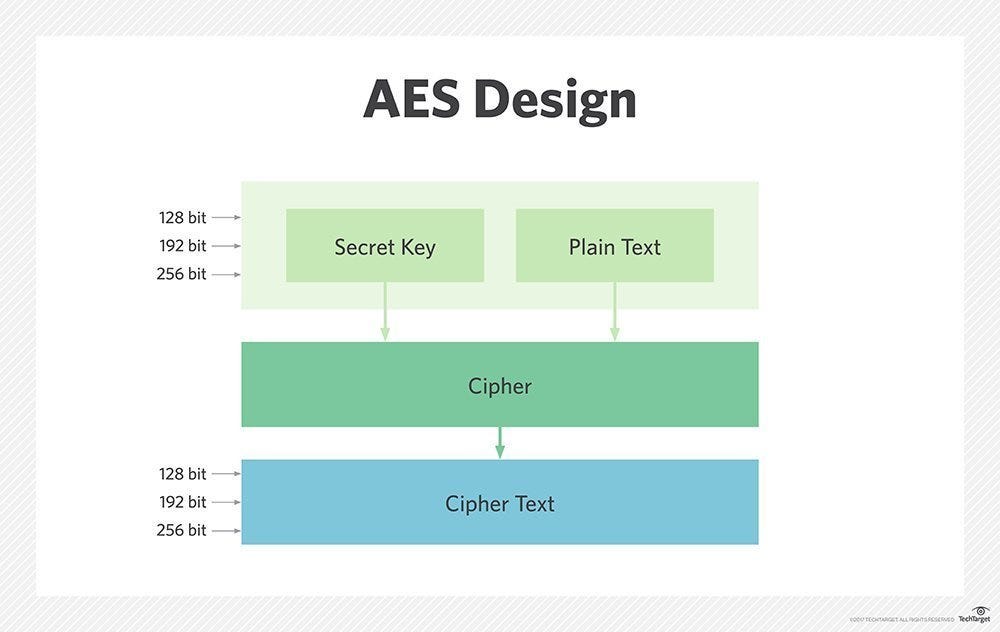
End-to-End Data Security:Shielding API Payloads through CryptoJS and Java AES-256 Encryption” | by Shivam Jaswal | Medium
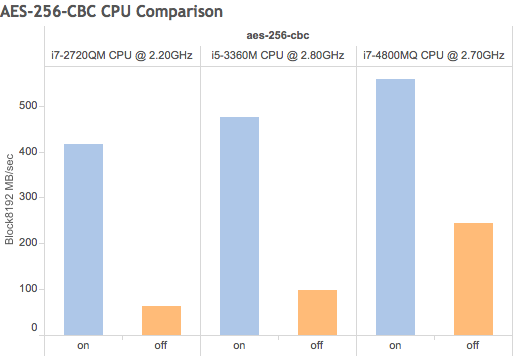
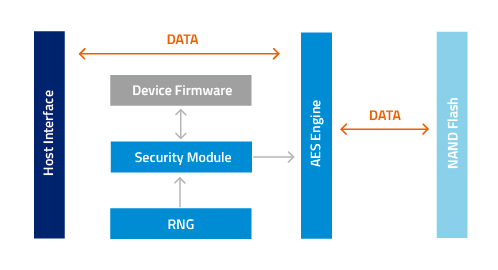
Using your existing hardware, Forward Secrecy and AES-NI to enhance system speed and security for free
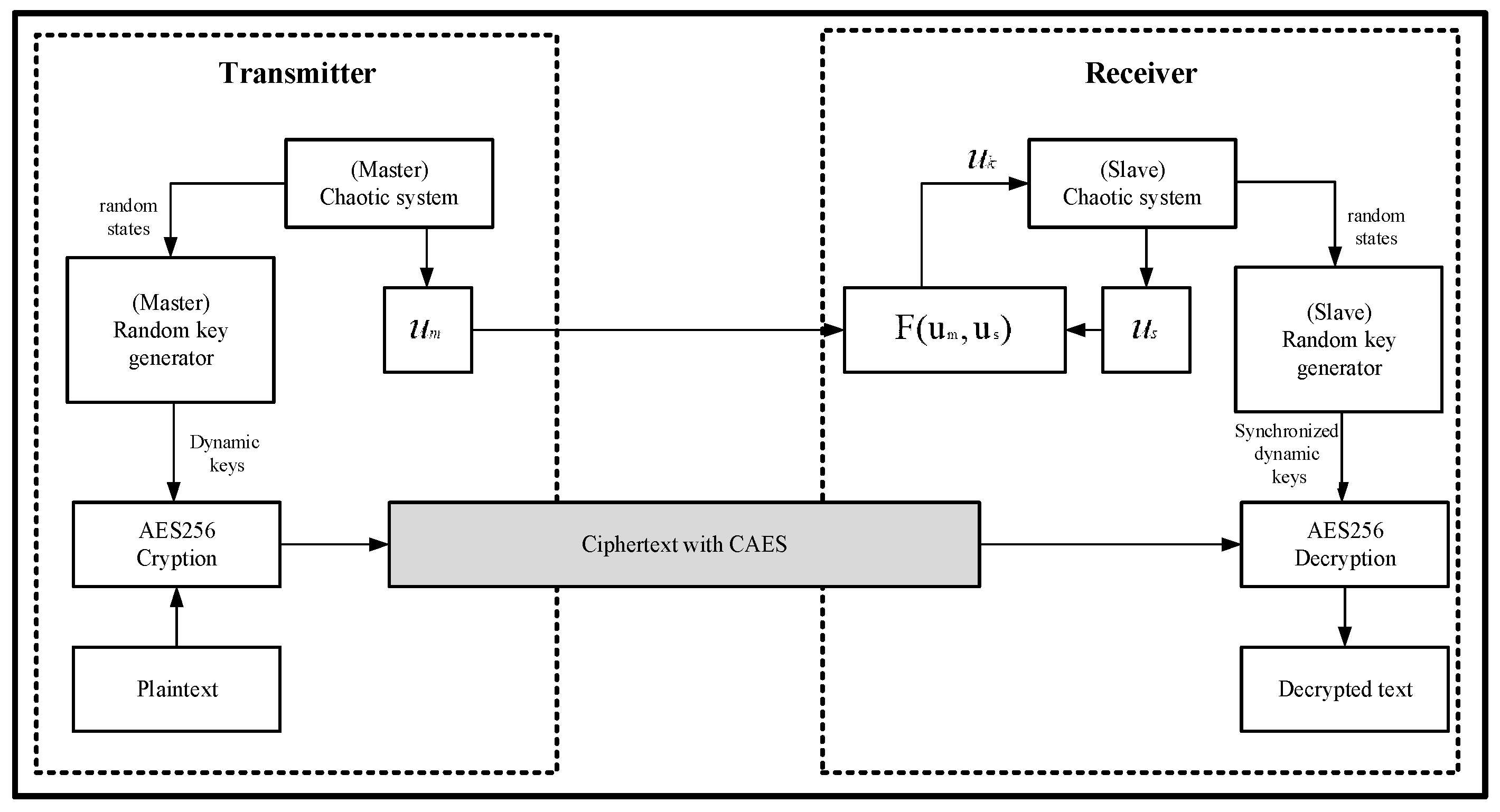
Applied Sciences | Free Full-Text | Chaos-Based Synchronized Dynamic Keys and Their Application to Image Encryption with an Improved AES Algorithm
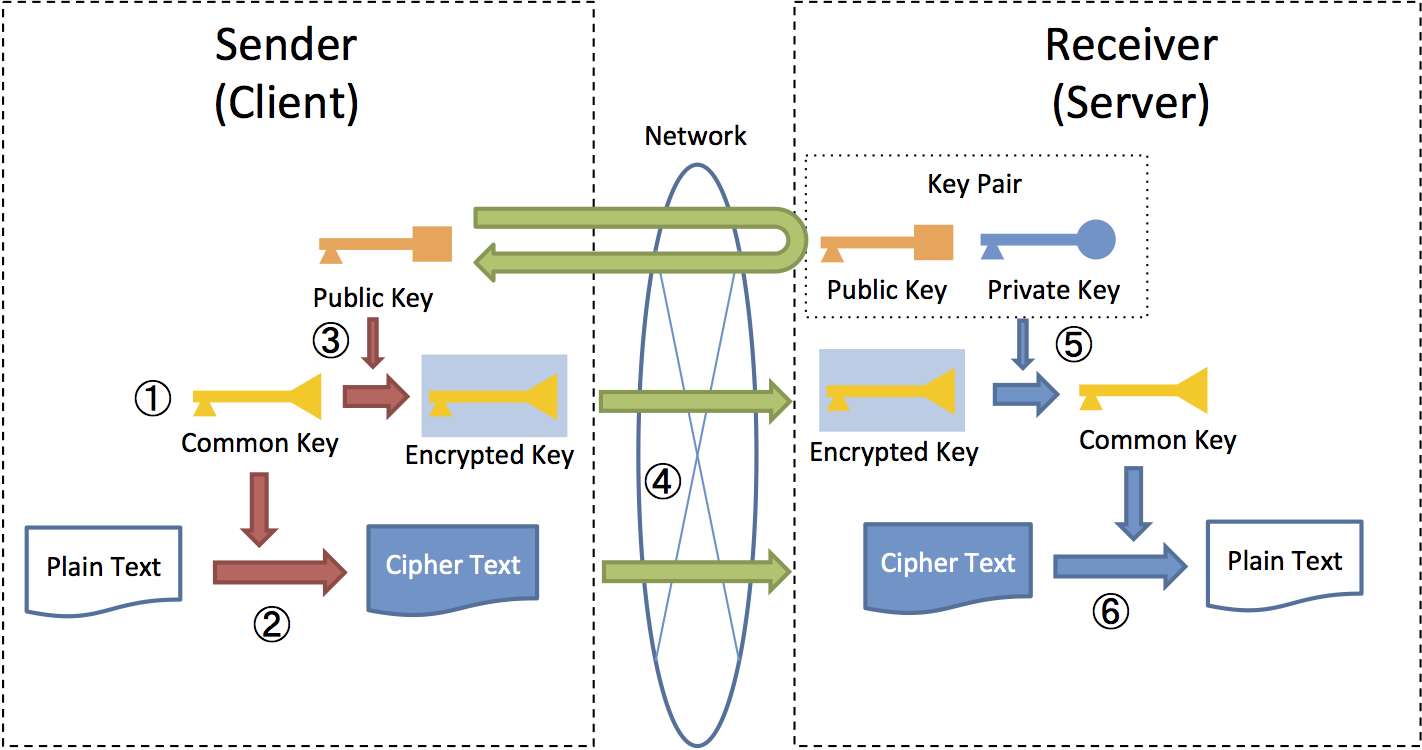
9.8. Encryption — TERASOLUNA Server Framework for Java (5.x) Development Guideline 5.3.1.RELEASE documentation

CBC (Cipher Block Chaining)-Based Authenticated Encryption for Securing Sensor Data in Smart Home | SpringerLink
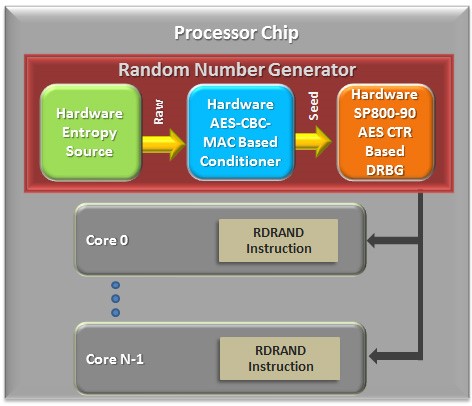
Intel® Hardware-based Security Technologies Bring Differentiation to Biometrics Recognition Applications Part 2 - CodeProject